
The bottom of the article has been updated with additional technical details about this campaign.
Amazon warns that Russian-speaking hackers used multiple generative AI services as part of a campaign to breach more than 600 FortiGate firewalls in 55 countries in five weeks.
According to a new report by CJ Moses, CISO at Amazon Integrated Security, the hacking campaign occurred between January 11, 2026 and February 18, 2026, and did not rely on an exploit to penetrate the Fortinet firewall.

Instead, threat actors targeted exposed management interfaces and weak credentials without MFA protection, and used AI to automate access to other devices on the compromised network.
Moses said firewall breaches were observed across South Asia, Latin America, the Caribbean, West Africa, Northern Europe, and Southeast Asia, among others.
Hacking campaign using AI
Amazon said it learned about the campaign after discovering a server hosting malicious tools used to target Fortinet’s FortiGate firewalls.
As part of the campaign, the attackers targeted FortiGate management interfaces exposed to the internet by scanning for services running on ports 443, 8443, 10443, and 4443. The targets were reportedly not specific to any industry and were opportunistic.
The attacker used a brute force attack with a common password to gain access to the device, rather than a typical zero-day attack that targets FortiGate devices.
Once infiltrated, the threat actor extracted the device’s configuration settings. This includes:
- SSL-VPN user credentials, including recoverable passwords
- Administrator credentials
- Firewall policies and internal network architecture
- IPsec VPN configuration
- Network topology and routing information
These configuration files were parsed and decrypted using what appear to be AI-assisted Python and Go tools.
“Following VPN access to the victim’s network, the attacker deploys different versions of custom reconnaissance tools written in both Go and Python,” Amazon explained.
“Analysis of the source code revealed clear signs of AI-assisted development: redundant comments that simply restate function names, a simplified architecture with a disproportionate investment in format over functionality, simple JSON parsing with string matching rather than proper deserialization, and built-in language compatibility shims with empty documentation stubs.”
“While this tool works for the attacker’s specific use case, it lacks robustness and fails in edge cases, which is typical of AI-generated code used without significant refinement.”
These tools were used to automate reconnaissance of compromised networks by analyzing routing tables, classifying networks by size, performing port scans using the open source Gogo scanner, identifying SMB hosts and domain controllers, and finding HTTP services using Nuclei.
The researchers said that while these tools worked, they commonly fail in more hardened environments.
The operational documentation, written in Russian, details how to use Meterpreter and mimikatz to perform DCSync attacks against Windows domain controllers and extract NTLM password hashes from Active Directory databases.
The campaign also specifically targeted Veeam Backup & Replication servers using custom PowerShell scripts, compiled credential extraction tools, and attempts to exploit vulnerabilities in Veeam.
One of the servers found by Amazon (212[.]11.64.250), the threat actor hosted a PowerShell script named “DecryptVeeamPasswords.ps1” that was used to target backup applications.
As Amazon explains, attackers often target backup infrastructure before deploying ransomware to prevent encrypted files from being restored from backups.
The threat actor’s “operational notes” also included multiple references attempting to exploit various vulnerabilities, including CVE-2019-7192 (QNAP RCE), CVE-2023-27532 (Veeam Information Disclosure), and CVE-2024-40711 (Veeam RCE).
The report said the attackers repeatedly tried unsuccessfully to break into patched or locked down systems, but instead of continuing to try to gain access, they moved on to easier targets.
Amazon believes this attacker has a low to moderate skill set, but that skill set has been significantly enhanced through the use of AI.
Researchers say the attackers utilized at least two large language model providers throughout the campaign to:
- Generate a staged attack technique
- Develop custom scripts in multiple programming languages
- Create a reconnaissance framework
- Plan your lateral movement strategy
- Draft operational documentation
In one instance, the attacker reportedly sent the complete internal victim network topology, including IP addresses, hostnames, credentials, and known services, to an AI service for assistance in further propagating into the network.
Amazon said the campaign shows how commercial AI services are lowering the barrier to entry for threat actors, allowing them to carry out attacks that are typically outside their skill sets.
The company recommends that FortiGate administrators do not expose their management interfaces to the internet, ensure MFA is enabled, ensure the VPN password is not the same as the Active Directory account, and harden their backup infrastructure.
Google recently reported that attackers are exploiting Gemini AI at every stage of a cyberattack, mirroring what Amazon has observed in this campaign.
Custom AI toolset powers breaches
A separate study published yesterday on the Cyber and Ramen Security Blog provides additional technical details about how AI and large-scale language models were directly incorporated into intrusion campaigns.
Researchers shared that the server at 212.11.64 was misconfigured.[.]250 were also discovered by Amazon and exposed 1,402 files including stolen FortiGate configuration backups, Active Directory mapping data, credential dumps, vulnerability assessments, and attack plan documents.
“Server at 212.11.64[.]250:9999, hosted on AS4264 (Global-Data System IT Corporation, Zurich, Switzerland), contained 1,402 files in 139 subdirectories,” the threat researcher explained.
“Folders within the directory contained CVE exploit code, FortiGate configuration files, Nuclei scan templates, and Veeam credential extraction tools. Claude-0 and Claude Between the two, there were over 200 files, including output from the load code task, session diffs, and cached prompt state. ”
“A folder titled fortigate_27.123(Full IP Redacted) held configuration data and credentials for what appears to be a compromised FortiGate appliance.”
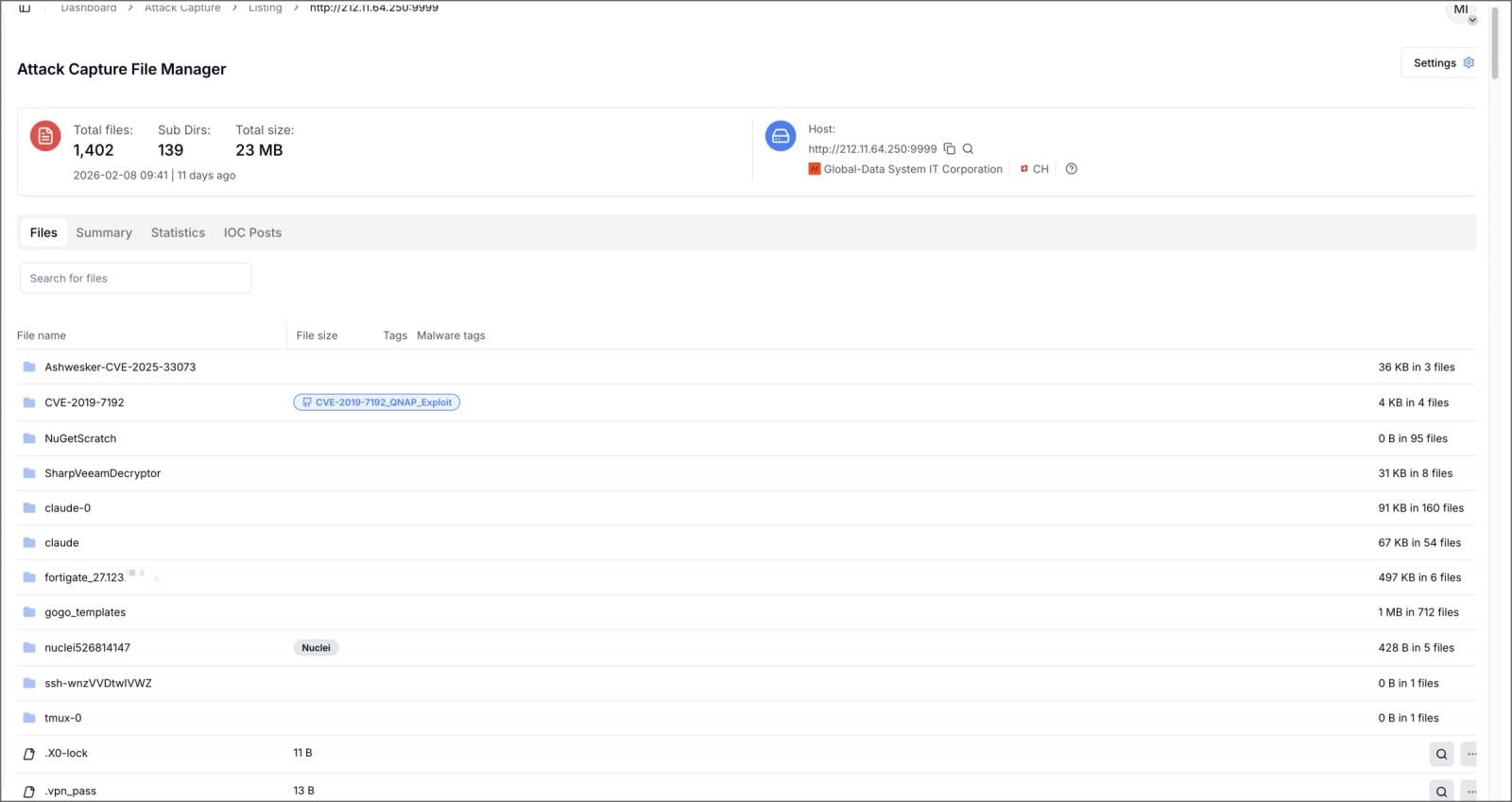
Source: Cyber and Ramen
The published files included a custom Model Context Protocol (MCP) server named ARXON that served as a bridge between reconnaissance data and commercial large-scale language models. Researchers said they found no public references to ARXON, indicating it is likely a custom MCP framework created by threat actors.
The MCP server acts as a middle layer that takes in data, feeds it to the language model, and uses the generated output in other tools. In this campaign, the captured data was used to automate post-breach analysis and attack planning.
Another Go tool called CHECKER2 is a Docker-based orchestrator used to scan thousands of VPN targets in parallel, with logs showing more than 2,500 potential targets spanning over 100 countries.
According to researchers, reconnaissance data collected from compromised FortiGate appliances and internal networks was fed into ARXON, which queried large language models such as DeepSeek and Claude to generate structured attack plans.
These attack plans included steps to obtain domain administrators, recommended locations to look for credentials, recommended exploitation steps, and guidance on lateral spread to other devices.
In some cases, Claude Code was configured to run offensive tools on its own, such as Impacket scripts, Metasploit modules, and hashcat, without requiring each command to be approved by the attacker.
Researchers note that the operation evolved over several weeks, with the attackers first using the open-source HexStrike MCP framework and moving to an automated and customized ARXON system about eight weeks later.
The report shares Amazon’s assessment that generative AI is being used as a multiplier, allowing attackers to scale their intrusions more efficiently. Researchers similarly warn that defenders should prioritize patching edge devices and auditing anomalous SSH activity and VPN account creation.
CronUp security researcher Germán Fernández also discovered another server publishing a directory containing what appears to be an AI generation tool targeting FortiWeb.
Although these tools do not appear to be part of the FortiGate campaign, they are yet another example of how threat actors continue to use AI tools to enhance their attacks.
Updated February 21, 2026: Added technical details from the Cyber and Ramen Security Blog and German Fernández.

Modern IT infrastructures are changing faster than manual workflows can handle.
In this new Tines guide, learn how your team can reduce hidden manual delays, improve reliability through automated responses, and build and scale intelligent workflows based on the tools you already use.




