
A new family of Android click fraud Trojans leverages TensorFlow machine learning models to automatically detect and manipulate specific ad elements.
This mechanism relies on machine learning-based visual analysis instead of predefined JavaScript click routines and does not involve script-based DOM-level interactions like traditional click fraud Trojans.
Threat actors are using TensorFlow.js, an open source library developed by Google for training and deploying machine learning models in JavaScript. You can use Node.js to run AI models in your browser or on your server.

Researchers at mobile security company Dr.Web have discovered a new family of Android Trojans being distributed through GetApps, the official app store for Xiaomi devices.
They discovered that this malware can operate in a mode called “phantom”. This mode uses a hidden WebView-based built-in browser to load click fraud target pages and JavaScript files. The purpose of the script is to automate actions on ads displayed on loaded sites.
After loading the trained model from a remote server, a hidden browser is placed on the virtual screen and a screenshot is taken for TensorFlow.js to analyze and identify relevant elements.
By tapping on the correct UI element, the malware reproduces the user’s normal activity. This method is more effective and resistant to the fluctuations of modern advertising, as most of these ads are dynamic, change structure frequently, and often use iframes or videos.
The second mode, called “signaling,” uses WebRTC to stream a live video feed of the virtual browser screen to an attacker, allowing the attacker to perform real-time actions such as tapping, scrolling, and text input.
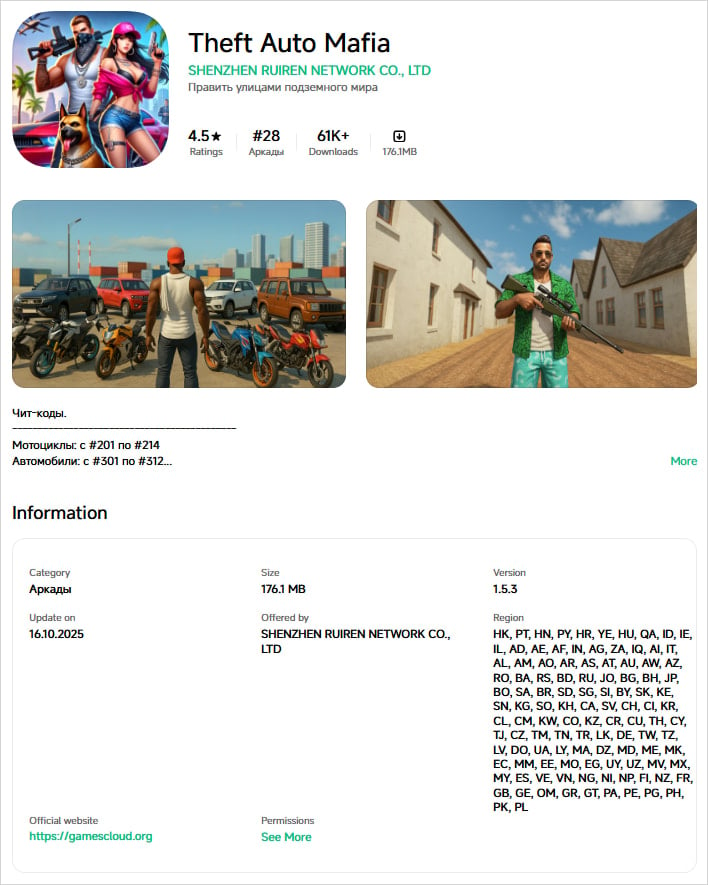
Threat actors distribute malware in games on Xiaomi’s GetApps software catalog. Initially, the app is submitted without any malicious functionality and receives the malicious component in a subsequent update.
Some of the infected games identified by Doctor Web are:
- theft auto mafia — 61,000 downloads
- cute pet house — 34,000 downloads
- creative magic world — 32,000 downloads
- amazing unicorn party — 13,000 downloads
- open world gangsters — 11,000 downloads
- Sakura Dream Academy — 4,000 downloads
Source: Doctor Web
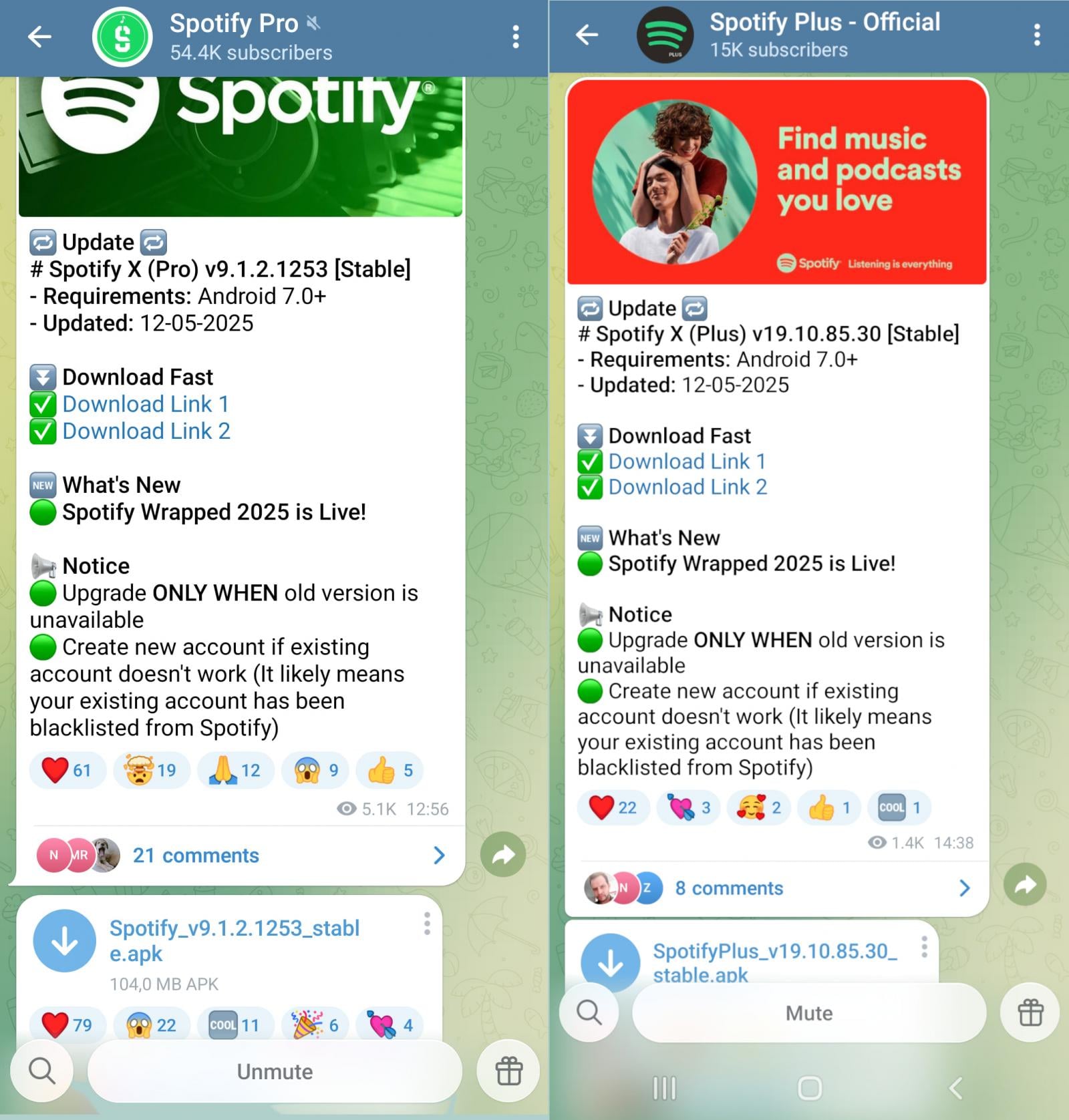
In addition to Xiaomi-hosted apps, Trojans are distributed via third-party APK sites (e.g. Apkmody and Moddroid, modified versions of the original Spotify, YouTube, Deezer, and Netflix apps, so-called MODs).
Researchers say most apps on Moddroid’s “Editor’s Choice” page are infected.
Infected APK files are also distributed through some app examples such as Telegram channels, Spotify Pro, Spotify Plus – Official, Moddroid.com, Apkmody Chat, etc.
Source: Doctor Web
Dr.Web also discovered a Discord server with 24,000 subscribers pushing an infected app called Spotify X.
The researchers note that at least some of these apps “actually work,” which alleviates user skepticism. Combined with the fact that click fraud is performed covertly in a hidden WebView that renders content on a virtual screen, this means that victims will never see any signs of malicious activity.
Clickjacking and ad fraud are not an immediate threat to user privacy and data, but they are lucrative cybercrime activities. The immediate impact on users is battery drain and premature aging, and increased mobile data charges.
Android users are advised not to install apps outside of Google Play, especially alternative versions of popular apps that promise free access to additional features or premium subscriptions.
Updated 1/23 – A Google spokesperson sent the following comment to BleepingComputer regarding the above:
“According to current detections, no apps containing this malware are found on Google Play. Android users are automatically protected from known versions of this malware by Google Play Protect. Google Play Protect is turned on by default on Android devices with Google Play Services. Google Play Protect can warn users and block apps that are known to exhibit malicious behavior, even if those apps come from sources outside of Play.” – Google spokesperson for

As Model Context Protocol (MCP) becomes the standard for connecting LLMs to tools and data, security teams are moving rapidly to keep these new services secure.
This free cheat sheet has 7 best practices you can start using today.



