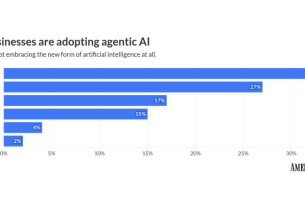
Agent-based artificial intelligence (AI) will transform the business landscape in the Asia Pacific and Japan (APJ) region in 2026, industry executives say. Organizations are expected to increasingly adopt autonomous software agents to increase both productivity and new categories of risk across business domains.
insider risk
Gareth Cox, vice president of APJ at Exabeam, highlighted the accelerating rate of adoption of AI agents. “According to research from IDC, 40% of organizations in Asia Pacific and Japan (APJ) are already using AI agents, and more than 50% plan to deploy AI agents within the next 12 months.As organizations embrace this change, they must rethink how they manage insider risk.Increasingly, insider risk does not just stem from rogue employees or compromised accounts, but also from AI operating autonomously with varying privileges. “Identities are creating a whole new category of insider threats, including malfunctioning agents that behave unpredictably, errant agents that follow flawed prompts that lead to compliance and privacy issues, or even subverted agents that can be weaponized by bad actors against your business.”
He cited a study by APJ’s cybersecurity experts, which expressed grave concern over the increasing number of incidents. “According to Exabeam research, 75% of APJ cybersecurity professionals report that AI has made insider threats more effective, and 69% expect insider incidents to increase in the next year, indicating the region is entering a phase where insider threats accelerate faster than traditional controls can keep up.However, most organizations are not adequately equipped to deal with growing insider risks.AI Not only is there no clear framework for managing agents, many organizations also use security tools.”The inability to capture behavioral patterns and decision-making in autonomous systems creates blind spots where AI agents can go undetected and take unintended actions. ”
He advised that establishing a baseline for both human and AI agent activity with real-time monitoring and explainable insights is essential to providing “the clarity, context, and control needed to protect against new types of insider threats.”
security framework
Security architecture is under scrutiny from a variety of perspectives. Michael Hubbard, chief customer officer at Ping Identity, suggested that 2026 will be a pivotal year for identity management. “As enterprises accelerate their AI strategies, 2026 will reveal a divide in how organizations approach the rise of non-human and agent identities. On one side are the teams that manage today’s human identity infrastructure and are carefully planning for a future where non-human identities (NHI) and agents will be an extension of that framework. On the other side are the teams that are often responsible for managing the enterprise’s trusted identities. We deploy agents quickly without linking them to the fabric.”
“The most advanced organizations will embrace these two camps to enable a new identity type (NHI) for their security teams. This collaboration will enable enterprises to securely scale while enabling AI agents to act, make decisions, and transact on behalf of humans within clearly defined trust boundaries,” Hubbard said.
David Haber, VP of AI Agent Security at Check Point Software Technologies, commented on the emergence of new governance needs. “2026 is the year that agent AI, autonomous systems that can reason, plan, and act with minimal human input, will go mainstream. We are moving from assistants drafting content to agents executing strategy. factories will self-diagnose failures and automatically order parts through a blockchain-verified network. Marketing, finance, and security functions will rely on agents that continuously learn from contextual data and operate at machine speed.”
“Autonomy without accountability is a liability. As agents gain operational authority, new governance gaps emerge: Who will examine their actions, audit their logic, and intervene when intentions diverge from results? Enterprises will need AI governance councils, strong policy guardrails, and an immutable audit trail to document all autonomous decisions,” said Haber.
Maury Haber, Chief Security Advisor at BeyondTrust, warned that the speed of AI adoption is outpacing previous waves of technology. He said increased attack surfaces and security issues, such as excessive privileges and poor security design, could have a direct impact.
Impact on operations
Sunitha Rao, general manager of hybrid cloud storage at Hitachi Vantara, sees automation extending to data management as well. “Intelligent policy-driven automation agents will increasingly take over repetitive operational tasks. These AI-driven agents manage tiering, compression, snapshot hygiene, and cost control while ensuring auditability, reversibility, and compliance. Guardrails and human oversight are maintained through ‘accountable automation’ logs that provide transparency and accountability.”
Kurt Senba, senior principal software systems engineer at Extreme Networks, emphasized the movement of agents to initiate and track actions, rather than just observing. Closed-loop processes automate 80% of repetitive IT operational tasks with escalation protocols that allow for secure and auditable intervention on exceptions.
Darryl Jones, vice president of consumer segment strategy at Ping Identity, noted that as agent AI transforms e-commerce, it will also change for consumers. “The rise of AI agents will continue to disrupt traditional e-commerce. This new channel will make consumers’ lives easier by eliminating the friction of working across organizations and multiple channels to complete a customer journey, whether it’s brainstorming a trip, booking that trip, traveling, and coming back to remember that trip.”
“The agent channel will also change the role humans play in the digital economy. As agents are increasingly empowered to make payments on behalf of users, organizations need to be prepared to leverage this new channel to acquire agent customers and understand that the omnichannel experience is truly evolving,” Jones said.
Supply chain and code risks
Jayant Dave, APAC field CISO at Check Point Software Technologies, pointed to new risk patterns enabled by hyperconnectivity. As companies integrate with vendors and third parties, agent AI has the potential to enable autonomous risk management. However, a compromised component can propagate risk throughout the ecosystem before the incident is detected.
Matias Madou, co-founder and chief technology officer at Secure Code Warrior, raised concerns about the readiness of agent AI for secure software development at scale. “Combining Agentic AI with MCP technology offers exciting new software development possibilities, but it is not safe to deploy in enterprise environments without security-skilled developers. Comprehensive data from BaxBench and others proves that, at least so far, LLM and Agenttic agents are still unable to produce enterprise-ready code, and even the highest-performing models contain errors and security vulnerabilities in 62% of delivered solutions.”
“We are sure to see further progress in this field in 2026, with exciting developments in MCP-powered scanning tools, access control tools, and other security weapons joining the arsenal. However, it will be quite some time before true secure and reliable autonomy is achieved. These all need to be carefully monitored by skilled security personnel and developers, who should be assessed and verified for security proficiency before using such powerful tools,” Madu said.