AI has not only changed the way we build, it has fundamentally changed the way we incur risk.
AI application is a dynamic, interconnected system that combines models, agents, tools, data, and infrastructure across code, clouds, and runtimes.
To maximize the value of these systems, organizations are connecting them to their production environments, allowing access to sensitive data, and enabling actions to be taken across the system. Here comes the risk.
Most approaches still analyze infrastructure, identities, and applications separately, leaving teams without the context they need to identify real risks.
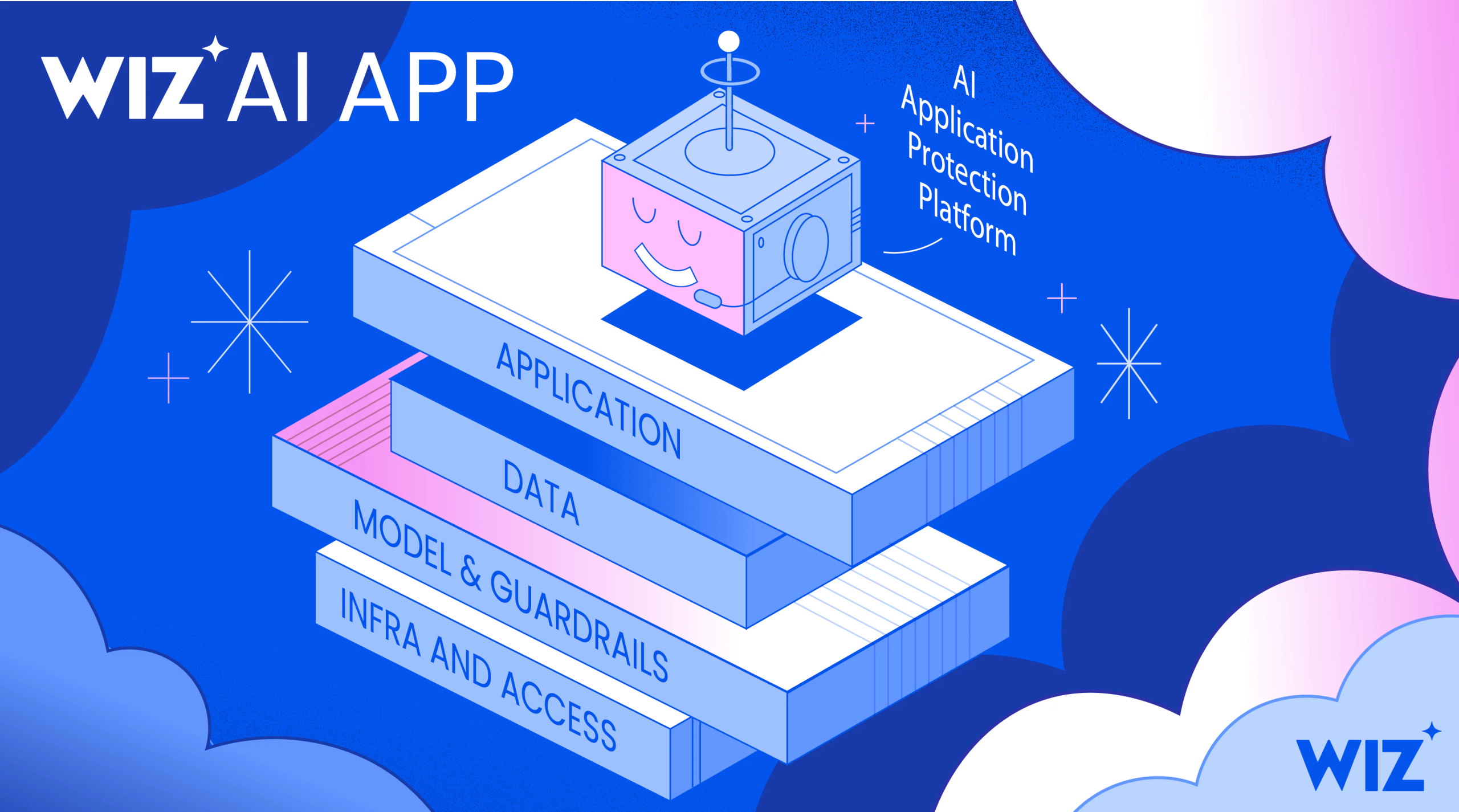
Today we will introduce: With AI Application Protection Platform (AI-APP) — Designed to protect your AI applications end-to-end with the context you need to understand and address real-world risks.
The context gap in AI security
Security teams are trying to answer:
-
Where are your AI applications running throughout your environment?
-
What are their abilities? What can they actually do?
-
Which of these actually represents an exploitable risk?
-
Can we detect and respond to threats across these AI applications in time?
because AI risk Don’t live in a single layer.
It emerges as systems interact between models, agents, tools, infrastructure, and data.
Consider a customer-facing AI chatbot connected to internal tools and data systems.
Attackers discover and exploit authentication bypass vulnerabilities (a common problem in rapidly built “vibecoded” applications). Insert a prompt, Manipulating an agent to cause it to behave in an unintended manner.
From there, the system works as designed, but with unintended consequences.
Each part of this activity looks as expected on its own.
-
Prompts are treated as regular model interactions
-
The agent executes code to retrieve sensitive data. This is the function the agent is designed to perform
-
The resulting access and data movement appears as valid cloud activity.
Only when these are connected will complete AI become a reality. Attack route becomes clear.
Introducing Wiz AI-APP
Wiz AI Application Protection Platform (AI-APP) unifies visibility, risk analysis, and runtime protection into a single graph-powered platform that enables teams to understand and protect AI systems in production. This is a natural evolution of the Cloud Native Application Protection Platform (CNAPP) as organizations increasingly build AI-native applications.
This enables teams to understand how to build AI systems, identify cross-layer risks, and detect and respond to threats in real time, all in one place.
1. Visibility — Build a complete AI inventory
AI adoption spans managed services, SaaS platforms, and custom-built applications, creating blind spots throughout the environment.
Wiz is complete inventory All AI applications use multiple detection methods:
-
managed platform — Tight integration with services like AWS Bedrock, Azure AI, Google Vertex AI, and more
-
Custom and self-hosted AI — Code and workload analysis to identify frameworks, agents, and services running in your environment
This important part is Wiz Workload Explainer — Use AI to discover and analyze how AI applications are built, turning custom implementations into distinct components that cannot be identified by deterministic scanning alone.
This enables Wiz to map AI systems end-to-end, regardless of their architecture, including models, agents, tools, and data flows. Our goal is to empower teams to build AI applications in the way that works best for them, while providing consistent security across it all.
In the chatbot example, this means identifying the agent service, the underlying model, connected tools, and the infrastructure on which it runs, even if not explicitly defined.
👉 See more details Visibility details.
2. Risk — Understand how risk manifests across hierarchies
AI risk is not defined by a single issue, but by how multiple conditions come together.
Wiz connects signals across the layers that make up AI applications.
Examples of chatbot risks include:
-
Infrastructure and access — AI agents are exposed through public endpoints with authentication bypass.
-
Models and guardrails — Agents run on AI models hosted in PaaS that do not have guardrails configured correctly.
-
Data — the model was trained on sensitive data
-
Applications — Agents have tools that allow them to read and expose sensitive data.
Individual layers may appear benign. Together, these define whether an attack is possible.
A key part of this understanding is how deeply Wiz analyzes the AI components. For example, Wiz tool Agents can use something like:
-
Read or publish data
-
Execute the code
-
Interacting with the API
-
Infrastructure changes
This is an example of Wiz’s continued understanding of AI-native risks over time. Wiz maps real exploitable attack paths by correlating signals between layers.
Wiz also maps AI risks to frameworks such as OWASP Top 10 for LLM Applications to help teams prioritize issues against real-world standards and compliance requirements.
👉 See more details Dig deeper into risk.
3. Runtime — Detect and respond to AI threats
AI systems are dynamic, and attacks unfold in real time.
Wiz provides threat detection across three complementary layers:
-
model activity — Monitor input, output, and prompt behavior
-
Executing the workload — Track agent execution, tool usage, and system activity
-
cloud layer — Observe identity usage, API calls, and infrastructure changes
In a chatbot scenario, this means:
-
Identifying prompted prompts that are manipulated in the model layer
-
Detecting code execution and behavior on host containers
-
Track credential usage and downstream activity in the cloud
This telemetry is connected to the full application context, allowing teams to: Detect threats early, understand whether activity represents real-world exploitation, and prioritize responses based on real-world impact.
👉 See more details Runtime details
Extend AI security beyond the Wiz platform
To extend this further, Wiz integrates with key WIN AI partners, bringing the intelligence of the AI security ecosystem to Wiz.
-
Cloudflare and Wiz By integrating to reveal which AI application endpoints are protected by Cloudflare’s AI Security for Apps and highlighting those that are left exposed, teams can prevent prompt injections, PII leaks, and Shadow AI.
-
TrojaAI and Wiz to bring AI red teaming findings from TrojAI into Wiz to uncover vulnerabilities such as jailbreaks, prompt injection exploits, and data leaks from AI endpoints. Wiz enriches these findings in a cloud context to uncover attack vectors to AI applications and helps teams prioritize exploitable risks.
-
Pillar security and with integrate and bring Pillar to Wiz blackbox agent red team assessment highlights vulnerabilities in public AI endpoints. By correlating these findings with existing risks across the environment, teams can gain visibility into exploitable paths and focus remediation on high-impact issues.
From insight to action
Understanding the risks is only part of the challenge.
Security teams need to operationalize this and put insights into action across engineering, security, and platform teams.
With Wiz, your team can:
-
Prioritize real risks based on full context
-
Forward the issue to the appropriate owner
-
Drive remediation with clear, practical guidance
It is powered by Wiz Agent, which acts as a power multiplier throughout the lifecycle.
-
red agent Reason like an attacker to identify complex risks that can be exploited
-
green agent Decide what to fix and who owns it
-
blue agent Investigate threats and verify real-world impact
We also extend this “insight into action” philosophy directly to AI-SDLC. By injecting Security Graph context into your AI development workflow, you can empower agents to go beyond generic suggestions. Alternatively, you can automatically identify misconfigurations, prioritize fixes based on cloud layer risk, and perform real-time remediation before code is committed.
Protect your AI at the speed of AI
AI is changing how systems are built and how attackers operate them.
Security must evolve with it.
Wiz AI-APP is built for this new reality.
-
Cross-layer context to understand how AI risks manifest in practice
-
Implementation-agnostic coverage across managed services, SaaS platforms, and custom-built applications
-
End-to-end visibility from code to runtime
Wiz AI-APP connects code, cloud, and runtime into a single platform, giving teams the context they need to understand and secure their AI systems end-to-end.
Secure AI applications — from code to runtime.